Correction appended
The leak of personal photos of more than 100 female celebrities, nude and otherwise, has tech observers questioning and debating potential vulnerabilities in Apple’s iCloud. But for those of us who don’t intuitively understand technology the questions remain: how could this happen and could it happen to me? Here are some answers:
Who was affected?
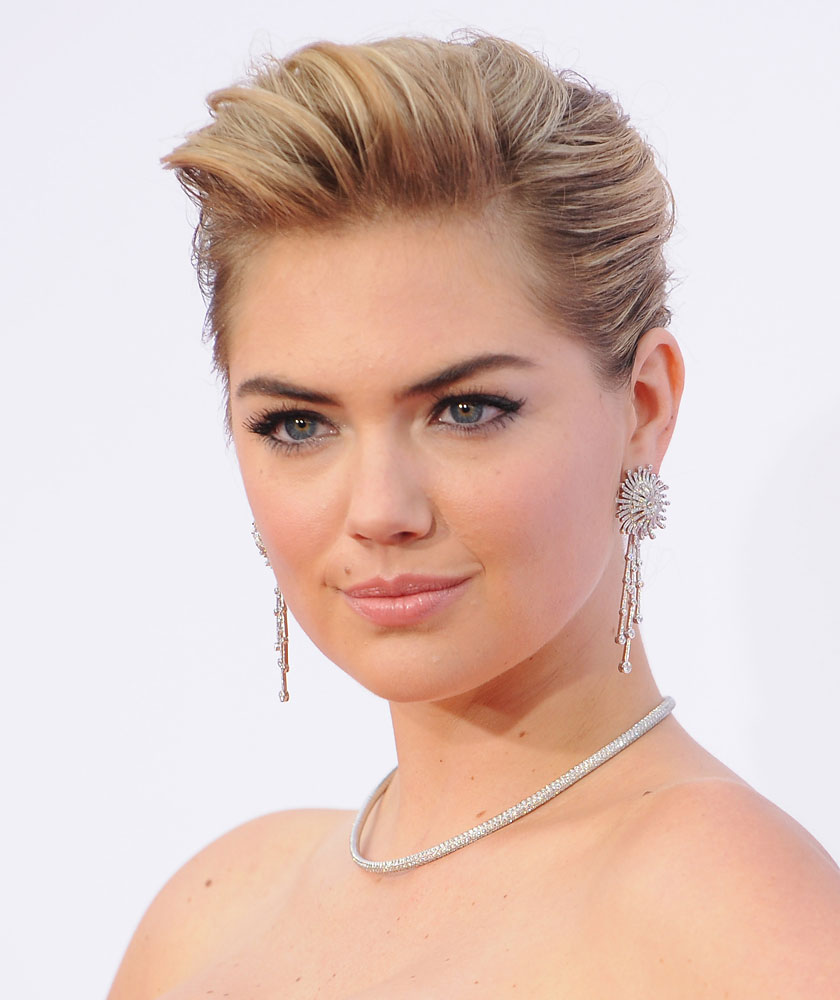
An anonymous user posted photos of celebrities like The Hunger Games star Jennifer Lawrence and model Kate Upton to the site 4Chan. The hacker claimed that there could be posts of more than 100 celebrities in total. Some celebrities, Lawrence and Upton included, confirmed the photos’ authenticity. Others, like Nickelodeon star Victoria Justice, claimed the photos were fakes.
How did the hackers do it?
The leading theory goes that hackers found a vulnerability in Apple iCloud’s “Find My iPhone” service, which helps users find lost or stolen phones via the cloud. Apple typically protects its products from so-called “brute force” programs that repeatedly guess random passwords for a given username until it gets a match.
But for some reason, various tech blogs have reported, Apple failed to do this with its Find My iPhone service. Hackers identified this vulnerability, TheNextWeb reports, and allegedly used a brute force service called “iBrute” to gain access to celebrities’ passwords — and consequently, the photos stored in their iCloud accounts.
Some tech observers are skeptical of this explanation, though. Most hacks occur through more straightforward methods of collecting a user’s personal data — via a lost cellphone owned by one of the celebrities, for example. There’s also evidence that some photos came from other devices that wouldn’t back up to the iCloud, like Android phones.
What does Apple have to say about all of this?
An Apple spokesperson told Re/code that the company is “actively investigating” the issue, but provided few other details. The company also reportedly rolled out a security upgrade Monday, just hours after the first hack, to eliminate the possibility of a brute force service gaining access to passwords via Find My iPhone.
Could this happen to me?
If the hackers did indeed use a brute force method on the iCloud and Apple has yet to fix the problem, then, in short, yes it could happen to you. Brute force methods can be applied so long as the hacker has your username. That said, this method does not collect broad amounts of data for a lot of people. Hackers would need a reason to target you specifically.
How do I protect myself?
The only way to completely protect yourself on the internet is to stay off it. But if you want to continue living in the 21st century, use two-step verification. Apple’s iCloud is just one of many services where you can set your account so that it asks you two personalized questions before you can access it. This makes it much, much harder for hackers to get where you don’t want them. Also, maybe think twice before uploading those nude photos?
The original version of this article misidentified the alleged role of code-hosting site GitHub in the data theft. Hackers reportedly used a code that was posted to the site.
More Must-Reads From TIME
- The 100 Most Influential People of 2024
- Coco Gauff Is Playing for Herself Now
- Scenes From Pro-Palestinian Encampments Across U.S. Universities
- 6 Compliments That Land Every Time
- If You're Dating Right Now , You're Brave: Column
- The AI That Could Heal a Divided Internet
- Fallout Is a Brilliant Model for the Future of Video Game Adaptations
- Want Weekly Recs on What to Watch, Read, and More? Sign Up for Worth Your Time
Write to Justin Worland at justin.worland@time.com