A version of this article was published in TIME’s newsletter Into the Metaverse. Subscribe for a weekly guide to the future of the Internet. You can find past issues of the newsletter here.
It’s the biggest financial seizure in the history of the U.S. Department of Justice: $3.6 billion in Bitcoin that the government says was stolen in a massive hack in 2016.
The announcement on Tuesday by federal law enforcement and prosecutors revealed a six-year chess match to find the culprits behind the theft of 119,754 Bitcoin from the cryptocurrency exchange Bitfinex. The proceeds—worth $72 million then, but $4.5 billion now—were siphoned from users’ accounts into a single crypto wallet.
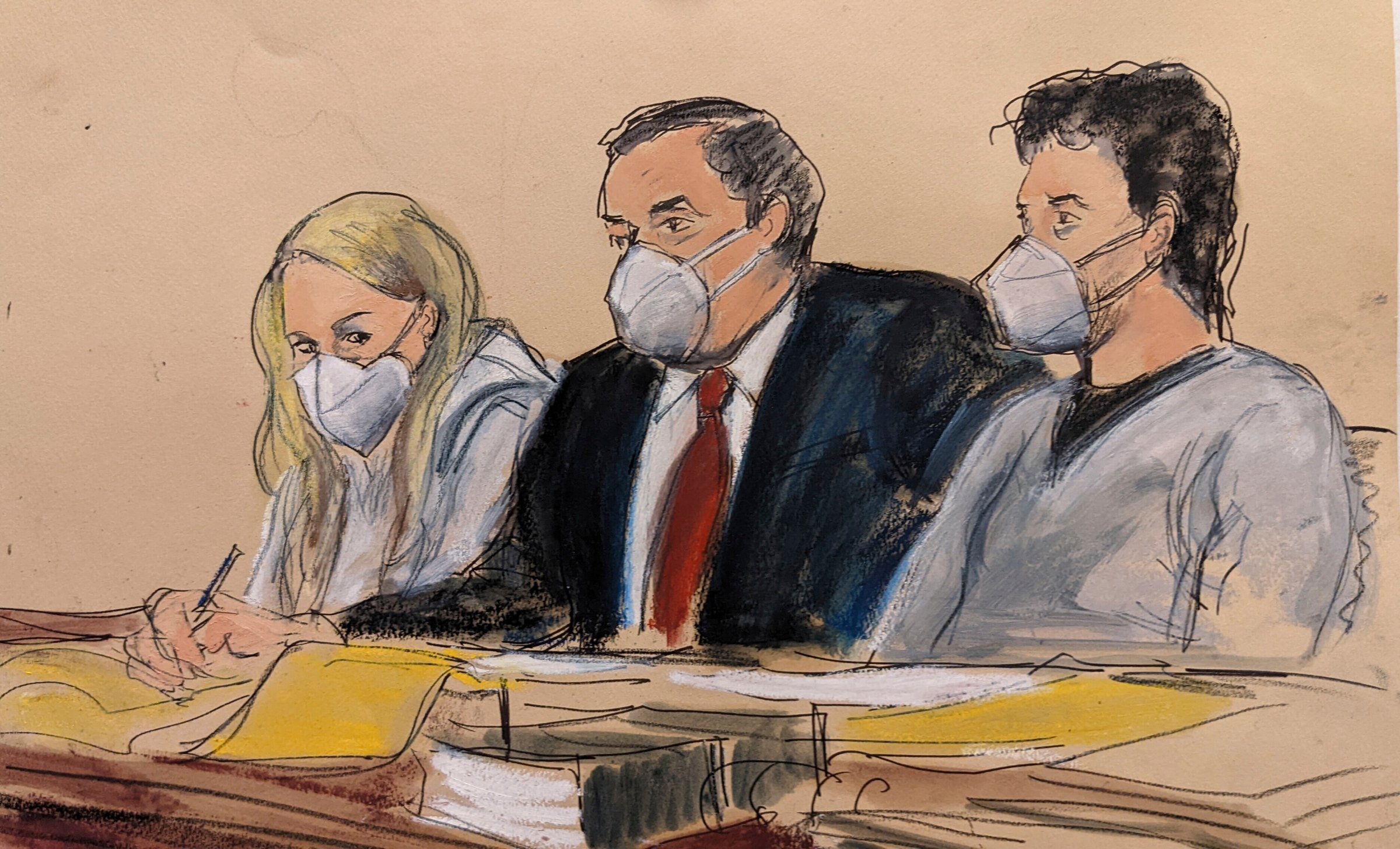
For years, most of the money sat in that wallet untouched. But, once the currency slowly began to move out of the wallet and into the traditional banking system, investigators were able to start tracing the transactions to people in the real world. On Tuesday, a married couple in New York, Ilya Lichtenstein and Heather Morgan, age 34 and 31, were arrested and charged with conspiracy to commit money laundering and conspiracy to defraud the United States.
The anatomy of Lichtenstein and Morgan’s alleged money laundering scheme—and how they got caught—is a cautionary tale in an era of rapid blockchain ascendancy. To get better insight into what happened, TIME spoke with two crypto security experts: Ari Redbord, the head of legal and government affairs at TRM Labs, a cryptocurrency regulatory startup; and Tom Robinson, a co-founder of the Blockchain analytics company Elliptic. Together, along with details in government affidavits they paint a picture of a crypto-savvy couple trying to stay one step ahead of the law and constant advances in blockchain tracking and security. Eventually, the painstaking detective work of government officials, and the innate transparency of the blockchain and its lack of red tape led to the arrests. “The problem with laundering cryptocurrency is if you make a mistake five years ago, that’s still on the blockchain for everyone to see,” Robinson says.
The hack
In the mid-2010s, Bitcoin became a tool for drug dealers, tax evaders, libertarians, and speculators alike to move money across the world outside of the watchful eye of traditional financial institutions. While the currency’s decentralized, unregulated nature was part of its appeal for many, those very traits also made the currency susceptible to attacks. The very first Bitcoin exchange, Mt. Gox, collapsed in 2014 after hackers exposed security loopholes and made off with $500 million in cryptocurrency.
In 2016, Bitfinex—one of the largest cryptocurrency exchanges at the time—suffered its own security breach. Some 2,000 transactions were approved from users’ accounts, sending the Bitcoin to one wallet. (A wallet is something like a decentralized bank account for cryptocurrency; they are unique to each user, but don’t have to be linked to a person’s real-world identity.) The hack upended the entire crypto ecosystem, with the value of Bitcoin plunging about 20% within hours.
It’s worth noting that neither Lichtenstein nor Morgan are accused of perpetrating the actual hack. “It’s potentially more difficult to prove the hack,” Redbord, who himself worked at the Attorney General’s office for 11 years, says.
The laundering
After the hack, the wallet in question had tens of millions of dollars worth of Bitcoin in a single account. But to extract it in large withdrawals would arouse plenty of suspicion. Most of the cryptocurrency was simply left in the account to appreciate in value.
In early 2017, small amounts of money began to exit the wallet through Alphabay, a currency exchange on the dark web that was often used to transact deals for drugs, weapons, and other illicit goods, according to investigators. By routing crypto through Alphabay, the trail of money on the blockchain itself would run cold. The launderers could then simply deposit the money in another Bitcoin wallet with its provenance obscured.
When Alphabay was shut down by law enforcement in 2017, the perpetrators switched to routing the money through the Russian-language marketplace Hydra, according to Tom Robinson at Elliptic, who has been tracking the money flow of the hack using tracing techniques and other software. Three years later, as Bitcoin prices spiked, the launderers employed a type of transaction known as a “coinjoin,” using Wasabi Wallet, a privacy wallet designed to prevent blockchain tracing. These methods amounted to the most “state-of-the-art laundering techniques” at the time, Robinson says.
Lisa O. Monaco, the U.S. Deputy Attorney General, alleges that it was Lichtenstein and Morgan who undertook these operations. According to Monaco’s statement, they used darknet services in conjunction with a series of complicated maneuvers that amounted to “a labyrinth of cryptocurrency transactions,” including opening accounts under false names, moving funds in thousands of small, separate transactions that were automated by computer so as to pass under the radar of financial watchdogs.
Eventually, the funds made their way into more traditional financial accounts held by Lichtenstein and Morgan, who spent the money on gold, NFTs and a Walmart gift card that was used to pay for Ubers and a Playstation, according to charging documents. A vast amount of Bitcoin—hundreds of millions of dollars worth—was converted into real money, but there was still a long way to go: 80% of the funds that had initially been deposited into the initial crypto wallet after the hack remained there until January 31.
The chase
As the launderers tried technique after technique to move the money, efforts to combat scammers were escalating—particularly in the U.S. Regulatory agencies were taking notice, investigating large scams. U.S.-based crypto currency exchanges were falling in line under the purview of the Department of Treasury, which required that they establish anti-money laundering (AML) programs and KYC (know-your-customer) protocols to make it harder for anonymous users to transfer money.
Meanwhile, crypto researchers and coders were building out more sophisticated tracking tools, hoping to bring some order and accountability to a space rife with scamming and bad actors. TRM Labs, for example, developed a tool to combat the effectiveness of “chain-hopping,” a set of actions in which launderers move funds rapidly across different blockchains (like converting Bitcoin to Ethereum to Solana). Elliptic, similarly, developed automated tracing techniques to track money across “peeling chains,” in which cryptocurrency is routed through a bevy of addresses. Last May, Robinson wrote a detailed blog post about the web of laundering from the Bitfinex hack money, complete with detailed graphics of where the money was ending up.
But while experts like Robinson knew which cryptocurrency accounts stored the stolen Bitcoin, linking blockchain addresses to actual people was another matter entirely. Robinson says that the Justice Department’s efforts were aided tremendously by the fact that AlphaBay had been shut down in 2017 by an international law enforcement effort led by the FBI. This shutdown, Robinson believes, gave law enforcement access to the service’s internal transaction logs, which helped officials concretely connect the dots between the wallet linked to the 2016 hack and the laundered accounts. “The fact that law enforcement took down AlphaBay probably led to [Lichtenstein and Morgan’s] downfall,” Robinson says.
With the biggest piece of the puzzle found, officials began finding links between the smaller shell accounts and bank accounts that belonged to Lichtenstein and Morgan, according to the charging papers. In January, they obtained a search warrant for a cloud storage account belonging to Lichtenstein, where they found a list of wallet addresses linked to the hack with their passwords. One of those wallets stored the majority of the remaining money: 94,000 Bitcoin, documents alleged. Using Lichtenstein’s passwords in the cloud, they entered the account and seized the funds, investigators said.
Redbord says the speed and force with which the investigation and seizure was carried out was aided by the transparent nature of the blockchain. “Law enforcement investigators have never had a more open way to follow the money,” Redbord says. “This shows cybercriminals that just because it’s years after a hack, don’t think you’ve gotten away with it: We’re going to trace those funds until we can seize them.” U.S. officials said that while a judge would ultimately decide how the recovered money would be distributed, the government would seek to return funds to their original owners.
This may only be the beginning of the DOJ’s efforts to crack down on crypto scams. The feds have been highly active, launching a National Cryptocurrency Enforcement Team last year to expand investigations of money laundering and other financial crimes. Last June, it recovered millions of dollars from the Colonial Pipeline ransomware attack. Meanwhile, other regulatory bodies, including the Securities and Exchange Commission (SEC) and the Commodity Futures Trading Commission (CFTC) are positioning themselves to get a piece of the regulatory action.
Redbord says that amid all of the fierce debate about regulation surrounding the cryptocurrency space, both online and increasingly in the halls of Congress, a lot of regulation is “already in place” to allow an oversight action like the one that just occurred. “Every exchange, every broker, every ATM, every custodian, is required by the Financial Crimes Enforcement Network [a bureau of the Department of the Treasury] to have a compliance program, to report suspicious activity,” he says.
“To me, this case says to the policymakers [in Congress] that law enforcement has the tools, the training and the ability to follow the flow of funds in crypto,” Redbord says. “This is not just an anonymous thing used only for money laundering and fraud. In fact, the blockchain itself can be a powerful tool for investigating financial crime.”
More Must-Reads from TIME
- Breaking Down the 2024 Election Calendar
- How Nayib Bukele’s ‘Iron Fist’ Has Transformed El Salvador
- What if Ultra-Processed Foods Aren’t as Bad as You Think?
- How Ukraine Beat Russia in the Battle of the Black Sea
- Long COVID Looks Different in Kids
- How Project 2025 Would Jeopardize Americans’ Health
- What a $129 Frying Pan Says About America’s Eating Habits
- The 32 Most Anticipated Books of Fall 2024
Contact us at letters@time.com