
A series of security flaws in popular video-conferencing service Zoom left its users vulnerable to spying, denial of service attacks from unauthorized sites, and the potential installation of malware, according to a report from security researcher Jonathan Leitschuh. In a statement, Zoom says it has since addressed the security issues through recent app updates, and will offer users more control over their video settings in a forthcoming update, along with a tool for removing all traces of Zoom from Mac devices should concerned users want to completely uninstall the app and its related services.
Leitschuh, who reported the issue to Zoom in March, detailed how the vulnerability exclusively affects Mac devices, allowing for any website to automatically start a Zoom call on a user’s computer, potentially enabling the webcam without permission. It also gave certain webpages the ability to perpetrate a denial of service attack — essentially spamming Zoom’s Mac users with requests to join an invalid call, freezing the machine. The issues stemmed from the additional installation of a web server by Zoom, which had been implemented to work around updates made to Apple’s Safari web browser requiring confirmation each time a user wants to join a Zoom meeting.
Zoom says users have always had control over the option to disable video, as a setting made when making their first Zoom call. “All first-time Zoom users, upon joining their first meeting from a given device, are asked whether they would like their video to be turned off,” the company said in its statement. “For subsequent meetings, users can configure their client video settings to turn off video when joining a meeting.”
Zoom says the decision to install a local web server was made to streamline the user experience as it applied to joining meetings, and that the company is “not alone among video conferencing providers in implementing this solution.” The company also said it found no evidence of any users being affected by either the webcam vulnerability or a denial of service attack.
But according to Leitschuh, the web server — which remains installed even when Zoom itself is removed from a Mac — is another angle of attack for malicious parties. Certain domains used by the web server to easily re-download the Zoom application were set to expire on May 1, affording someone the (theoretical) opportunity to purchase the domain name and use it to infect computers reinstalling the app. After Leitschuh alerted Zoom to the issue on April 26, the company renewed the expiring domains.
“In order to fully protect users, I truly believe that this localhost web server solution needs to be removed,” said Leitschuh in his report. “According to the Zoom team, the only reason this localhost server continues to exist is that Apple’s Safari doesn’t support URI handlers.” At the time of publication, Zoom has not confirmed any plans to revise its use of local host servers.
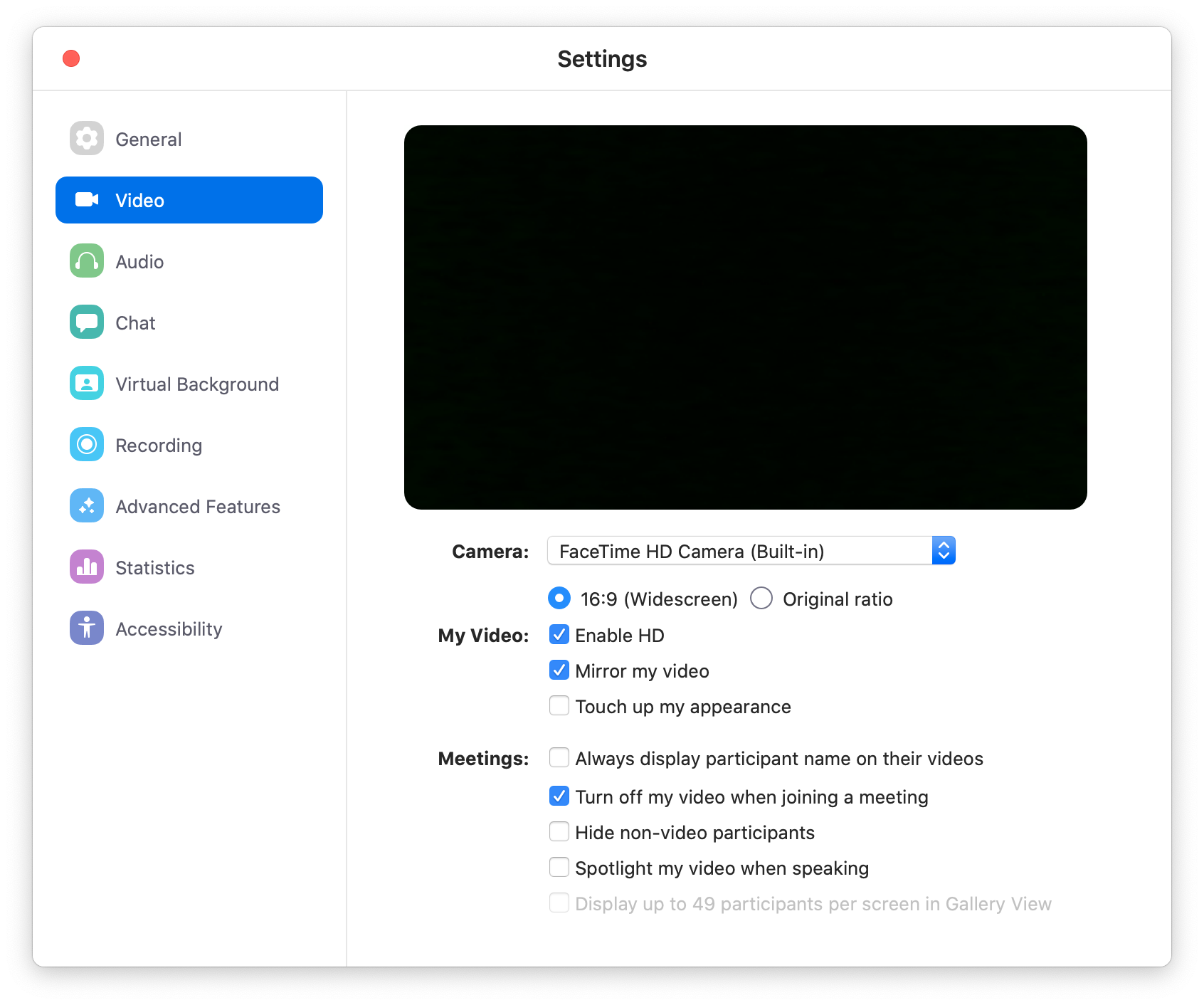
While those using Zoom on company-owned machines — usually managed by an office’s IT administrator — may not have the ability to uninstall Zoom themselves, changing the settings related to your webcam is easy enough. In your Zoom app’s Settings page, check the box “Turn off my video when joining a meeting,” which will disable automatic webcam activation.
If you’d rather remove Zoom from your Mac entirely, it’s possible, though you’ll need to do a little digging. While you can uninstall the Zoom app (simply drag the Zoom app from your Applications folder into your Mac’s trash can), the Zoom web server will persist on your Mac.
In an email to TIME, a Zoom spokesperson said users looking to remove Zoom from their Macs entirely would have to delete both the app and the Zoom local web server app manually. “By this weekend we will introduce a new app to help user easily delete both apps,” said Zoom. Otherwise, for users familiar with the Mac’s Terminal app, Letischuh outlines how you can disable the web server yourself.
More Must-Reads From TIME
- The 100 Most Influential People of 2024
- Coco Gauff Is Playing for Herself Now
- Scenes From Pro-Palestinian Encampments Across U.S. Universities
- 6 Compliments That Land Every Time
- If You're Dating Right Now , You're Brave: Column
- The AI That Could Heal a Divided Internet
- Fallout Is a Brilliant Model for the Future of Video Game Adaptations
- Want Weekly Recs on What to Watch, Read, and More? Sign Up for Worth Your Time
Write to Patrick Lucas Austin at patrick.austin@time.com