Google is adding another layer of security to Android by periodically checking users’ Google Play Store apps for malware.
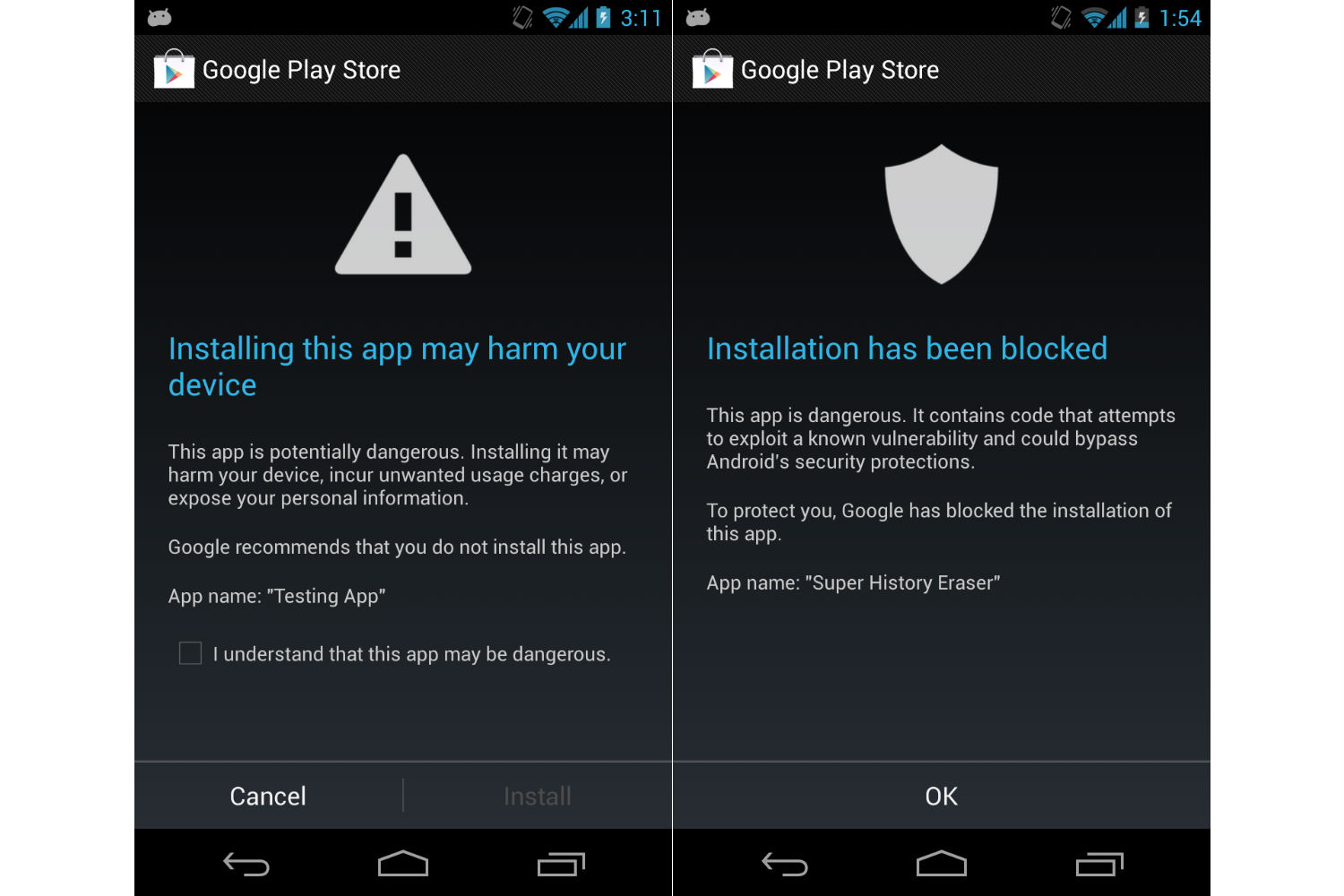
The new malware scanner in Android is an extension of Google’s “Verify Apps” tool, which in the past has only scanned apps from outside of Google Play, and only upon installation. The updated version will perform routine checks even after an app is installed, regardless of where it came from. If the scanner detects an app that’s potentially harmful, users will see a warning and an option to remove the offending app.
Google already scans apps before letting them into the Google Play Store, using a tool called “Bouncer.” But Bouncer doesn’t exist on users’ devices, and doesn’t scan apps that users have installed already. It’s also not foolproof, for a variety of reasons. With the new malware scanner, Google can keep a closer eye on apps that users are actually running on their phones and tablets.
In an interview, Android security head Adrian Ludwig said not to expect any significant impact on system resources. The scanner will be triggered by behaviors that are potentially harmful, such as premium text messages and root access, but otherwise will check in every couple days or so. “It’s very, very lightweight, and not something we’d ever expect a user to interact with,” Ludwig said.
Ludwig wouldn’t say how many users have been infected by malware through Google Play Store apps in the past, and said that any data from the malware scanner rollout is still too preliminary to share. But he did say that for apps outside of Google Play, users only installed them 0.18 percent of the time after being warned about potentially malicious behavior. Google expects that most users will never come across a warning.
It’s worth noting that many of the questionable Android apps that have made headlines recently would not fall under the malware scanner’s purview, because Google doesn’t view these apps as harmful to users.
For instance, Virus Shield, a $4 app that purported to wipe out security threats but actually did nothing, would not be detected by Google’s Verify Apps tool. Although Virus Shield was a scam, the app itself didn’t cause any further harm once users had purchased it. (Google has removed Virus Shield from the Play Store, and users can request refunds in these kinds of situations.)
Verify Apps also wouldn’t have picked up on Google Play Store apps that are secretly mining Litecoins and Dogecoins on users’ devices. Two such apps were discovered this week by security firm TrendMicro, and they’ve since been removed from the Google Play Store.
The issue in that case appeared to be that the apps weren’t disclosing their behavior, but Ludwig defended cryptocurrency mining in general as a potential business model for developers. “I think cryptocurrency is an extraordinarily good example of innovation happening that could not happen on a platform that blocks first and allows later,” Ludwig said. He added that the industry will have to think about how to disclose and implement cryptocurrency mining, and some of those practices may not be appropriate for Google Play, but he defended Android’s ability to let developers experiment.
Google’s attitude toward what constitutes malware underscores the divide between the company and third-party security firms, who sell their own apps to combat threats on Android. As another example, a popular flashlight app that secretly tracked users’ locations and sold the info to ad networks would probably not be flagged by Verify Apps, but many third-party tools will detect such behavior and send a warning to users.
While security firms do tend to overstate Android security risks — particularly by pointing out obscure apps or apps from outside of Google Play — they also offer a level of protection that Android on its own does not. (Google, for what it’s worth, sees the availability of these tools as a benefit of Android.)
Verify Apps is part of Google Play Services, which means users don’t have to do anything to add it to their devices. It’s enabled by default, but users can disable it by going to Google Settings > Verify Apps or Settings > Security > Verify Apps, depending on the Android version. The new malware scanner is rolling out gradually, and will be available on devices running Android 2.2 or higher.
More Must-Reads From TIME
- The 100 Most Influential People of 2024
- The Revolution of Yulia Navalnaya
- 6 Compliments That Land Every Time
- What's the Deal With the Bitcoin Halving?
- If You're Dating Right Now , You're Brave: Column
- The AI That Could Heal a Divided Internet
- Fallout Is a Brilliant Model for the Future of Video Game Adaptations
- Want Weekly Recs on What to Watch, Read, and More? Sign Up for Worth Your Time
Contact us at letters@time.com